TryHackMe DarkMatters - Write-Up
Let’s Start#
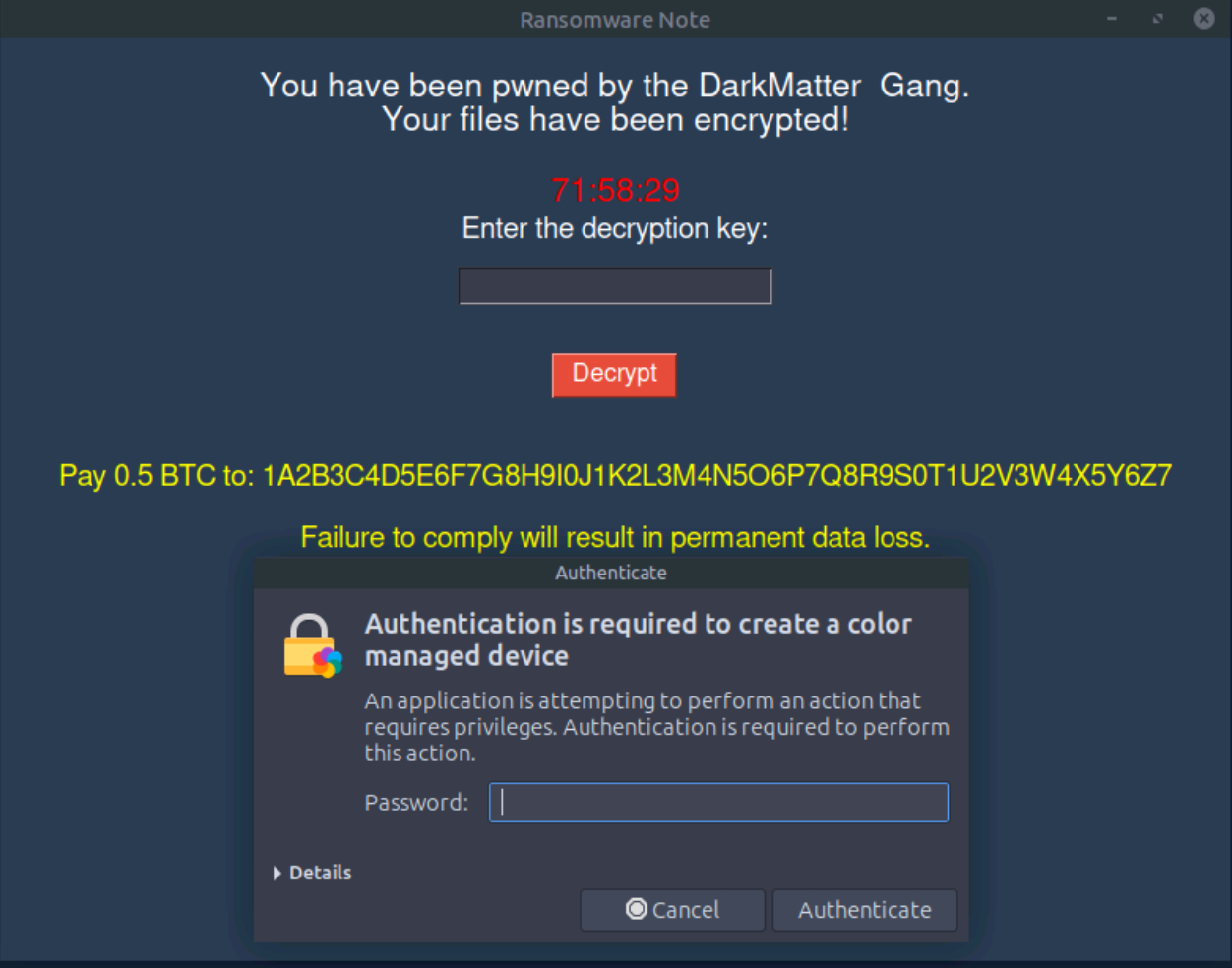
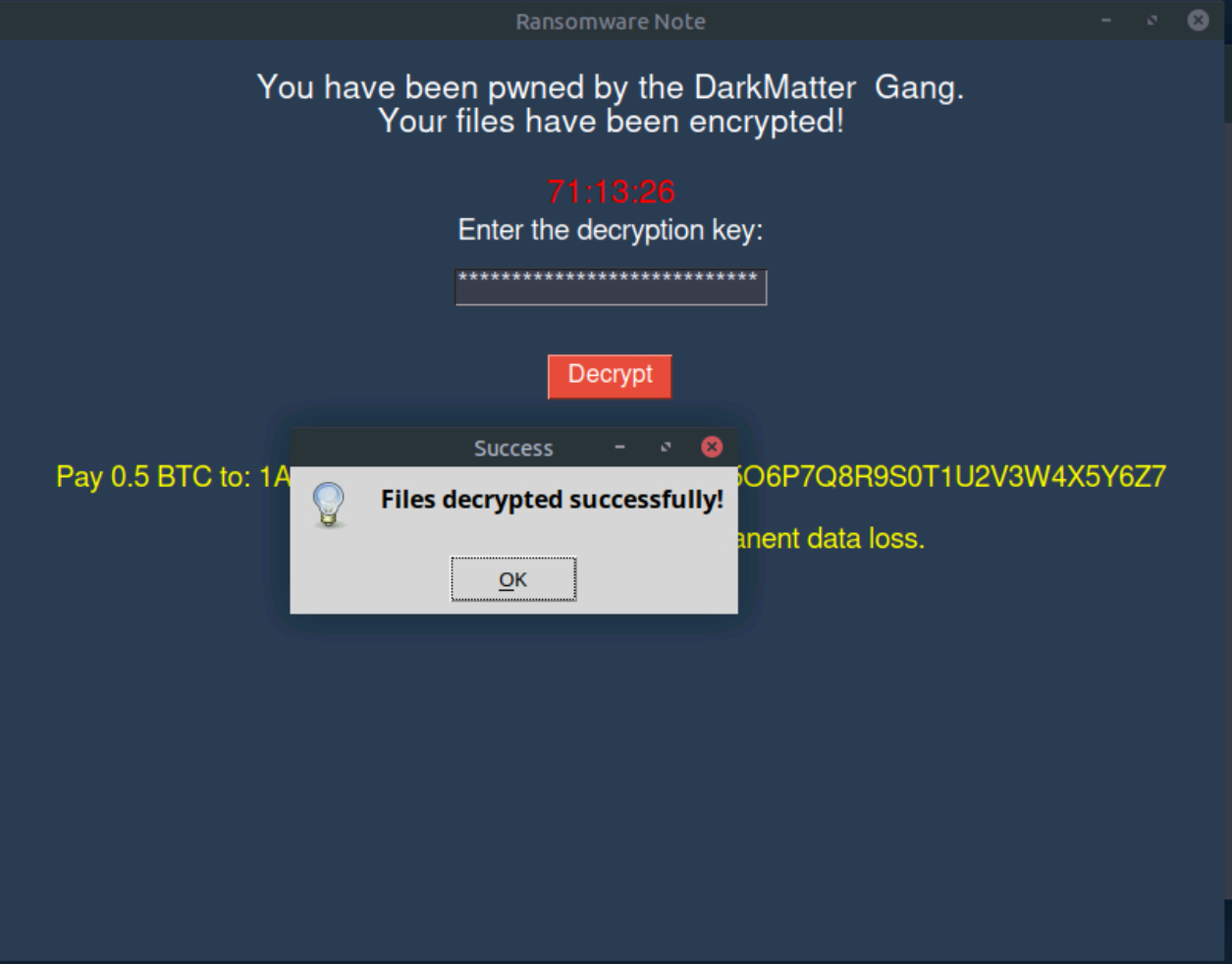
We are welcomed with a message that nobody wants to see… Our files are encrypted by the DarkMatter Gang. At the price of BTC right now we might need to find another solution !
Looking for Clues#
The attackers appear to have left some traces in /tmp.
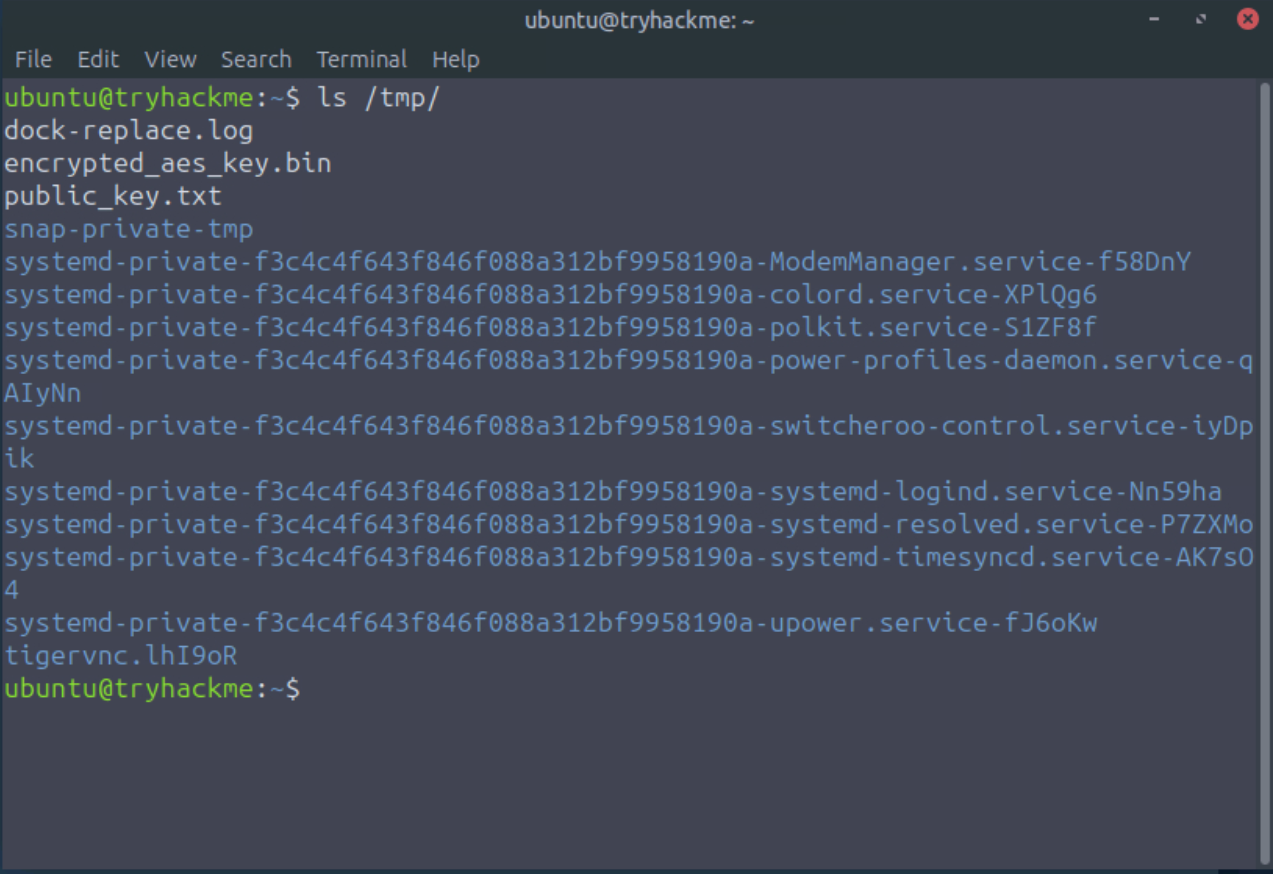
Two files immediately stand out:
public_key.txtencrypted_aes_key.bin
As the name encrypted_aes_key.bin suggests, the AES key has itself been encrypted. AES is a symmetric block cipher, which means it encrypts data in fixed-size blocks using a secret key. Without that key, the encrypted files remain unreadable.
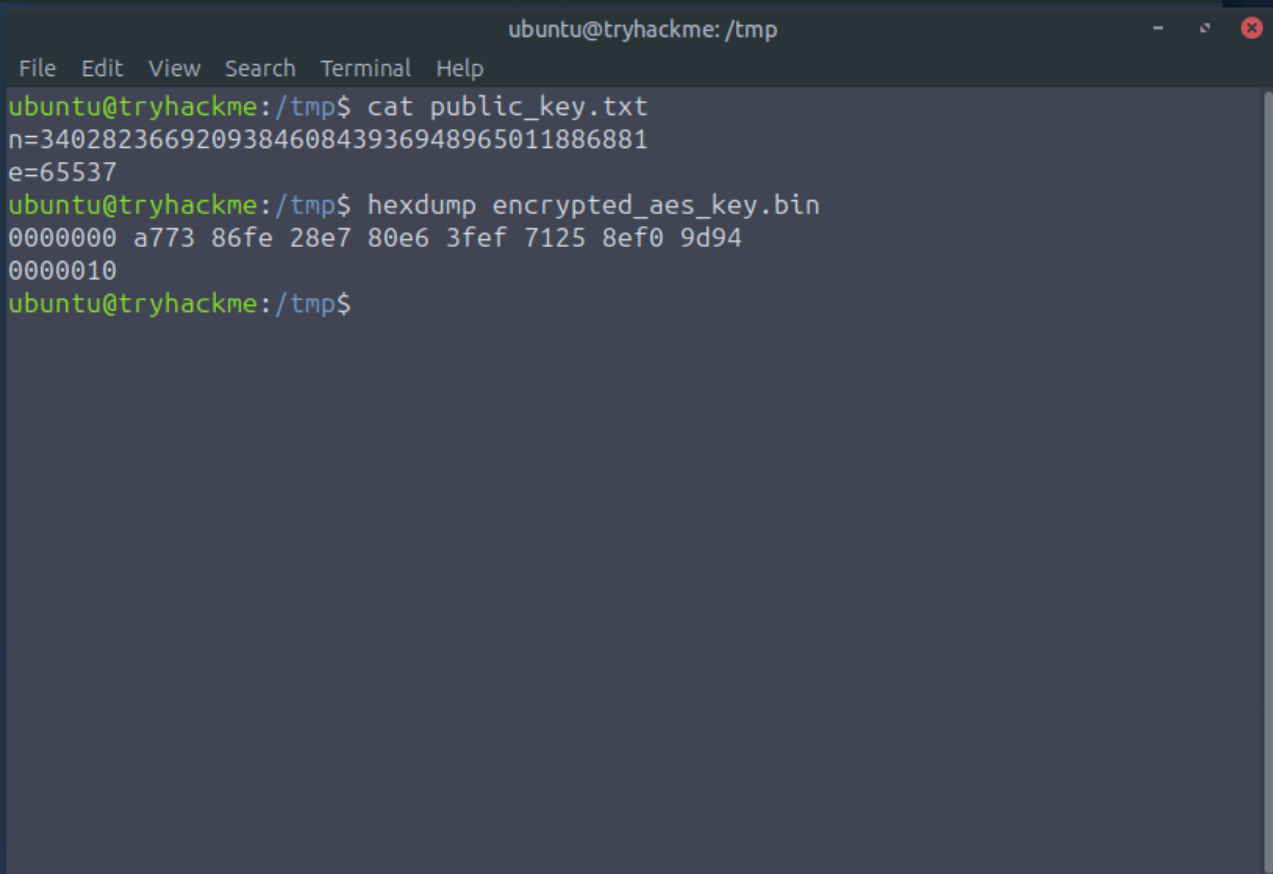
The values n and e belong to RSA, which was used here to encrypt the AES key. If we can recover the private exponent d, we can decrypt the AES key through modular exponentiation.
The weakness is clear: the RSA modulus is far too small. RSA security relies on the difficulty of factoring a large modulus n = p × q. In this challenge, however, n is only 128 bits, which makes factorization trivial. Once p and q are recovered, computing the private key becomes straightforward.
Recovering the Private Key#
Here is a snippet of code i wrote to recover the RSA private key:
from math import isqrt
def fermat_factor(n: int):
a=isqrt(n)
if a*a < n:
a+= 1
while True:
b2 = a*a-n
b = isqrt(b2)
if b*b == b2:
p = a-b
q = a+b
return p,q
a += 1
def extended_gcd(a: int, b: int):
if b == 0:
return a,1,0
g,x1,y1 = extended_gcd(b, a%b)
x = y1
y = x1-(a//b)*y1
return g,x,y
The overall idea is simple:
- Factor
nintopandq - Compute
φ(n) = (p - 1)(q - 1) - Recover the private exponent with
d ≡ e⁻¹ mod φ(n)
This was pretty easy as i already did it in my university cryptography course.
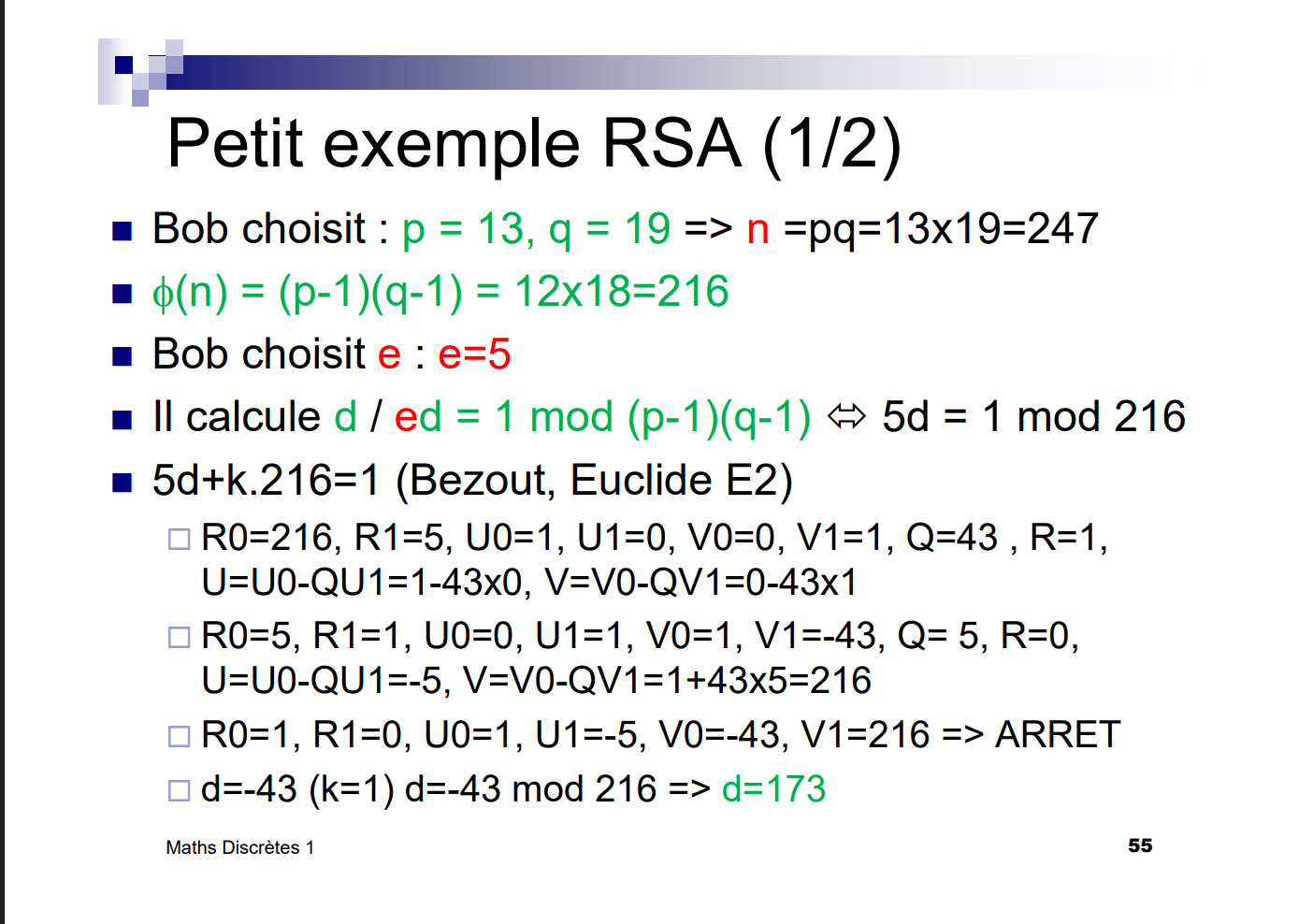
Course Reference#
These two course slides summarize the RSA logic used here:
| RSA slide 1 | RSA slide 2 |
|---|---|
 |
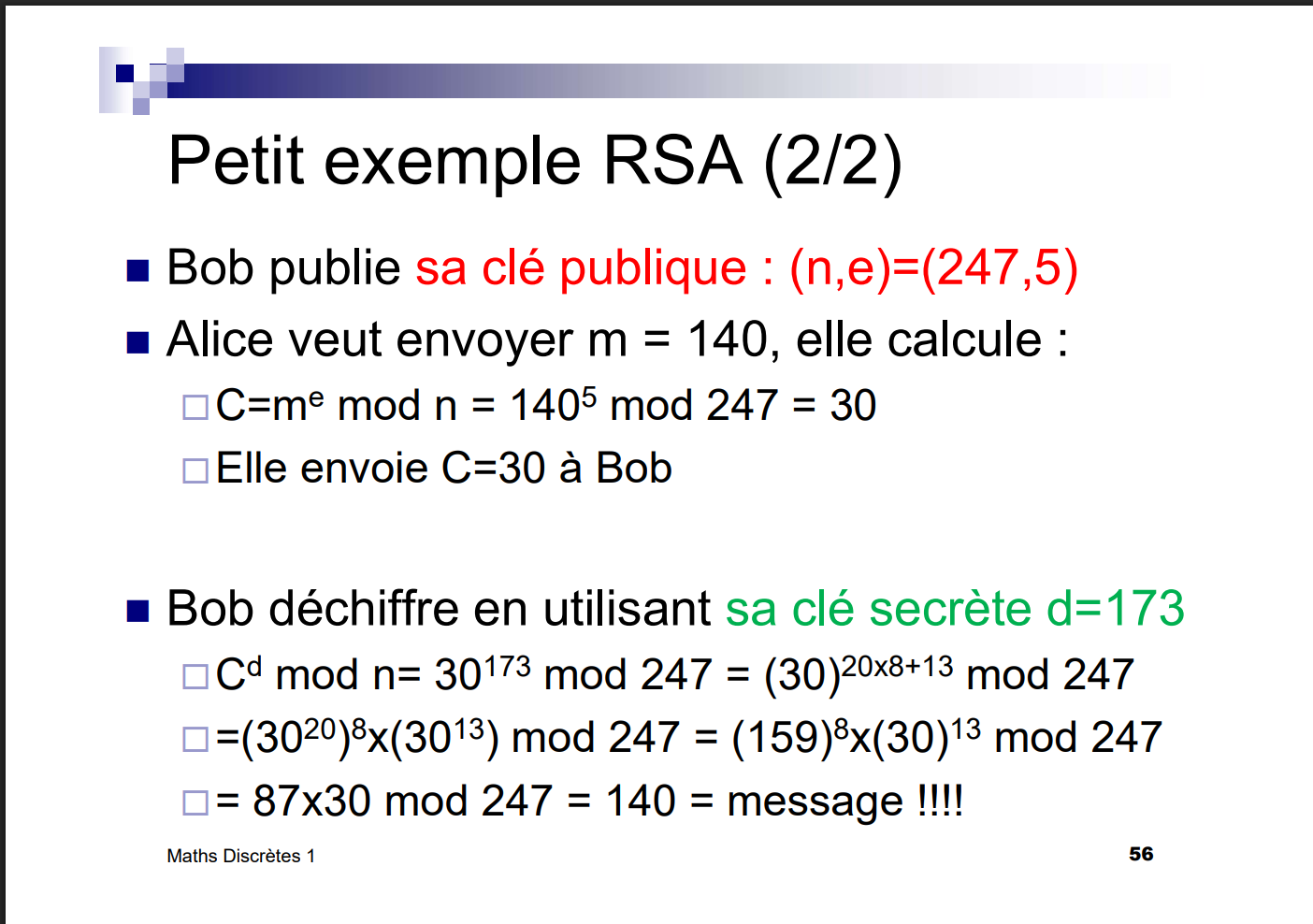 |
Using this approach, I recovered the RSA private exponent:
d = 196442361873243903843228745541797845217
Using d#
At that point, the ransomware interface accepted d directly, which allowed the files to be recovered.
From a cryptographic point of view, the proper process would have been:
- Decrypt the RSA-encrypted AES key using
m = c^d mod n - Use the recovered AES key to decrypt the files
Flag#
And here is the final flag:

Conclusion#
This was a fun challenge because it let me apply concepts from my cryptography course in a practical scenario.
The RSA implementation was clearly very weak. A 128-bit RSA key is BROKEN as my teacher says and should never be used in practice. Modern RSA deployments should use at least 2048 bits.